There have been numerous supply chain attacks in recent years that have revealed the precarious state of the vendor supply chain. A supply chain attack refers to a cyberattack that impacts a trusted third-party vendor that offers software or services to a variety of other organizations. The goal behind this type of attack is for hackers to infect or breach an application of an unsecured vendor in the supply chain to access their business partners, steal information, and commit fraud and other criminal activities. The real prize for the threat actors launching supply chain attacks is to identify those vendors that work with large enterprises, which can then be their cash cow if they are able to breach those enterprise businesses through the vendor.
It is often harder and takes more finesse and skill to compromise the systems of large companies that employ sophisticated security controls. Enterprise businesses these days, especially ones with access to huge amounts of personal data and confidential information, invest a lot of money in protecting those valuable assets. This is particularly true for massive public companies that are held accountable to their investors and must disclose cybersecurity incidents.
Threat actors know that many smaller vendors have weak security, making them easier to hack. And once hackers compromise these vendors, they can find ways to gain access to the larger companies with whom these vendors work. Enterprise businesses can only protect themselves from cyberattacks in so far as they have control over the security of their systems and processes. But when it comes to external vendors that are integrated into their tech stack or business processes, larger enterprises have no way of ensuring that these smaller businesses have the same security protocols in place or uphold the same security standards. Unsuspecting enterprises, therefore, have become vulnerable to attacks through their unsecure vendors in the supply chain, which can have deleterious effects.
When does this happen?
Supply chain attacks are becoming more widespread, and the risks are increasing every year. According to Cybersecurity Ventures, $60 Billion will be lost to software supply chain attacks By 2025. In a press release last year, Gartner estimated that 45% of organizations worldwide will experience software supply chain attacks by 2025. There have been a number of glaring examples that have occurred in the past years.
One of the more notable supply chain attacks over the past few years was the Solarwinds assault. This was a fairly typical supply chain attack. As a third-party supplier to many customers, Solarwinds was an ideal target for threat actors looking to gain access to their network of clients, which the hackers achieved by injecting malicious code into Solarwinds’s monitoring and management software, Orion. Even now, years after the initial attack, the fallout continues to be extensive.
Another example from earlier this year is the hack of the MOVEit Transfer application, which compromised hundreds of organizations in both the private and public sectors worldwide. As a result of using the MOVEit program to transfer information and shared files, hundreds of businesses were compromised by the attack and the personal data of tens of millions of people have been exposed.
What is particularly troubling here is the fact that these cases are the harbinger of many more sophisticated supply chain attacks and attempts to come, and the estimated losses are huge.
Supply Chain Attacks: A Real Risk To Business payments
Supply chain attacks are made possible by the simple reality that in today’s business world, every company relies on third parties and external partnerships to run their business. Every single company works with vendors, from large suppliers to even the smallest of agencies and individuals. And for all businesses, there is always a level of risk that comes with working with any third-party vendor.
Vendor management is complex, especially for businesses that work with hundreds or thousands of third-party suppliers. The more vendors a company has, the more susceptible they are to attacks because each of those vendors are a potential point of compromise. From our experience at Trustmi, when it comes to vendors there is always a high incidence of business email compromise (BEC) and other cyberattacks, and generative AI has made these attacks more sophisticated and effective. From a fraud perspective, the high quality of these attacks has made it almost impossible for people to tell the difference between real vendor communications and fraud attempts.
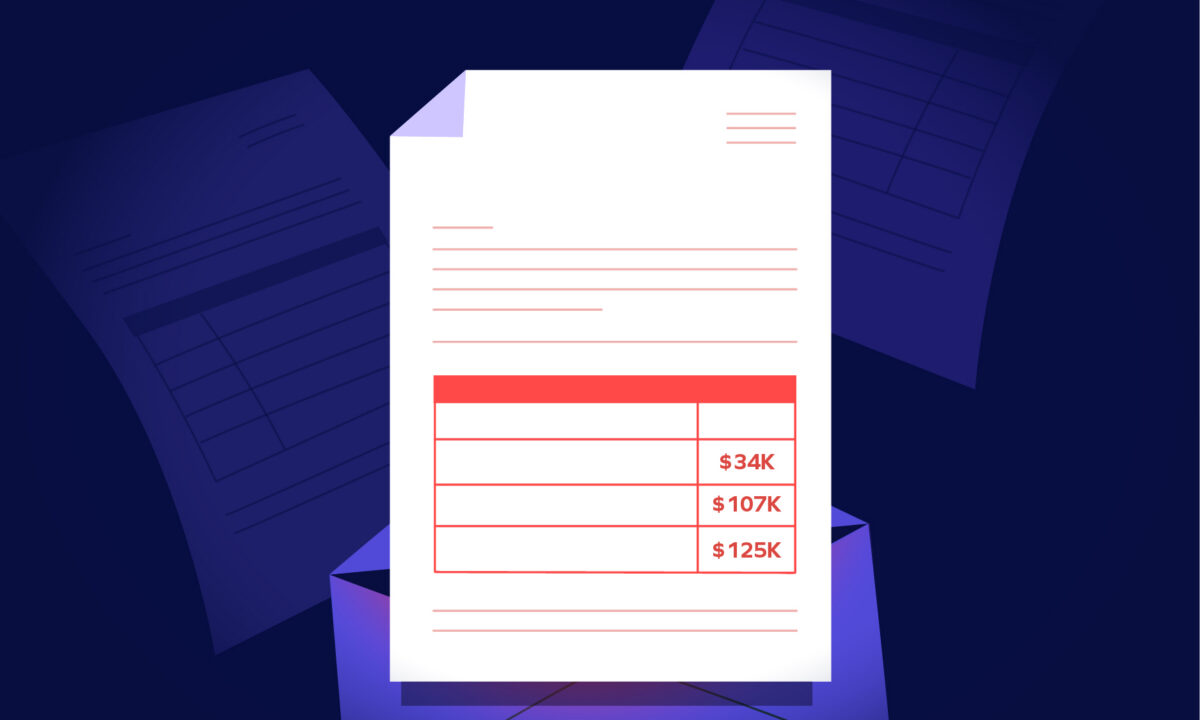
We also know that one of the leading areas of vendor compromise is business payment fraud. At Trustmi we see this happening time and time again through supply chain attacks. From vendor impersonation to direct attacks on ERP systems, the goal is to change vendor information to divert funds away from the real vendor to the fraudster.
Where Controls Fail
The current approach to protecting the supply chain, unfortunately, isn’t working. Currently risk management is assessed through a questionnaire that is filled out when a vendor first begins working with a company. During this process, the security team or Chief Information Security Officer receives a request from someone within the organization asking them to assess the vendor. At the time the vendor is first reviewed, the scope of the vendor’s access to sensitive information is specific and typically limited. However, the assessment process doesn’t take into account that the vendor’s access to confidential data or the scope of their work may increase over time. When this happens, security teams are not alerted and therefore do not run an updated security assessment to ensure the vendor is meeting security requirements for increased access. In this way, companies open themselves up to attacks by not monitoring and enforcing proper security protocols and controls for their vendors.
What Real Supply Chain Protection Looks Like
To fully protect themselves from supply chain attacks, companies must use AI technology that can efficiently manage and secure every vendor in the supply chain. The right solution must identify all vendors, provide full visibility into vendor management, monitor vendor activities, track and control their permissions and access to internal systems, and enforce security practices in addition to managing vendor profiles and changes to their payment information. Trustmi offers a comprehensive solution that does all this and more. Our Vendor Onboarding module is an easy self-service portal to help set up vendors securely and add them to our Trust Network. Our Vendor Lifecycle Management module strengthens the security of your supply chain, so you can have confidence that your vendors are always protected.
Contact us today to see a demo of our Vendor Onboarding and Vendor Lifecycle Management modules and learn how they can help you streamline and secure the management of your supply chain.








 Behavioral AI-powered security
Behavioral AI-powered security Protection on day one
Protection on day one 10-15x ROI
10-15x ROI